SSH keys
Introduction
A private-public key pair allows one to a access remote server via SSH with a preset encryption key, rather than just a password. Key pairs can be generated with ssh-keygen on Linux and PuTTYGen on Windows. When a key pair is generated, a passphrase may be created. If there is a passphrase set, then ssh-agent on Linux or Pageant on Windows can be used for logging in without needing to type the passphrase. This article explains how to use these tools in order to log in to a remote server using SSH and not typing a password.
Windows
First, you should make sure you have the Pageant and PuTTYGen programs downloaded. If you already have PuTTY and you installed it via an automated installer program, then it is likely you already have these. You should be able to find them in the directory in which PuTTY was installed. If you do not have them, you can grab both from the PuTTY downloads page: https://www.chiark.greenend.org.uk/~sgtatham/putty/download.html. There are lots of websites, many more legitimate looking than the official site, distributing malicious copies of the PuTTY tools due to its popularity, make sure to always download from the official website linked previously.
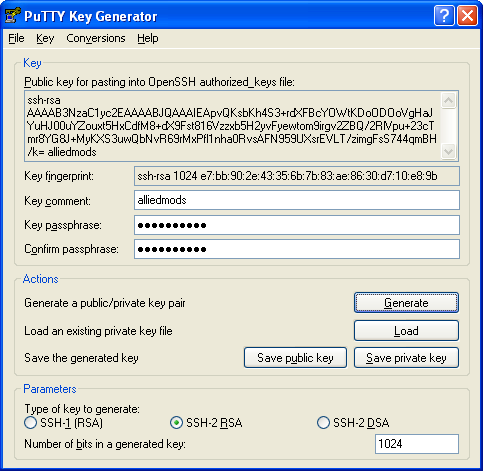
Open PuTTYGen first and click the button labeled "Generate." It will then ask you to move the mouse cursor over the blank area on the program's window (in order to generate some randomness for the keys). Then it will ask you to enter a comment (which is already filled, but may be changed) and the key's passphrase twice. You may leave this passphrase blank if you never wish to enter any kind of password for accessing the server via SSH. However it might be a good idea to enter something there for extra security. When using Pageant, you will only have to enter this passphrase once per Windows login. Your PuTTYGen window may look like this:
Click the button labeled "Save private key" and save this key somewhere on your computer, such as your My Documents directory. Right click in the area that shows your public key and select "Select All" from the menu. Then right click again and select "Copy."
Next, open a terminal window (with PuTTY or some other program) to the server that you wish to access using this key pair. Navigate to your home directory if you are not already there, and look for a directory named .ssh. If you do not have this directory, then create it like so:
cd ~ mkdir --mode=700 .ssh cd .ssh
Now you can go into this directory and type echo. Then right click on your terminal window. This should then paste your public key into the window. Then type a space after your public key followed by >> authorized_keys and press the enter key. Here is an example:
echo mypastedkey >> authorized_keys
Lastly, make sure your authorized_keys file has the correct permissions, or else it will not load. You can do this with:
chmod 600 authorized_keys
Now you should open Pageant. An icon for the program should appear in your system tray. Right click on this icon and select "Add Key" from the context menu.
A file dialog box will appear. Find and select the private key file that you saved earlier. If you chose to use a passphrase, it will ask you to enter it once. If you did not have a passphrase, then the key will be added automatically.
Now you may access the server via SSH in any way (such as using TortoiseSVN) without having to enter a password again. If you reboot your computer, or log out of your Windows session and log back in, you only have to open Pageant and add your key file again.
Linux
First, a private-public key pair must be created. You can do this by using ssh-keygen, which comes with openssh (which should already be installed). Type "ssh-keygen -t rsa". You will be asked to type a path to the file that will be created. You can press enter here because the default is usually fine. You will then be asked for the passphrase twice. As mentioned in the Windows section above, this is optional. You may leave this passphrase blank (by pressing enter when it asks) if you wish to use the keys without having to type a password. However, it might be a good idea to use one for extra security. When using ssh-agent, you will only have to enter this passphrase once per login.
Here's an example of what may occur with ssh-keygen:
damagedsoul@sente ~ $ ssh-keygen -t rsa Generating public/private rsa key pair. Enter file in which to save the key (/home/users/damagedsoul/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/users/damagedsoul/.ssh/id_rsa. Your public key has been saved in /home/users/damagedsoul/.ssh/id_rsa.pub. The key fingerprint is: 69:11:bb:1f:9b:e4:52:53:e1:75:30:75:b5:d2:c1:ba [email protected]
There should now be a file named id_rsa.pub in the .ssh directory of your home directory. Upload this file to the home directory of the server you wish to access using scp or some other means. Start an SSH session with the remote server and then navigate to your home directory if you are not already there. Then you can add the contents of id_rsa.pub to your authorized_keys file in the .ssh directory. If you do not have an .ssh directory, then you will have to create it.
Here is an example of the above information:
scp ~/.ssh/id_rsa.pub [email protected]:~/ ssh [email protected]
These next commands are then executed on the remote server:
cd ~ mkdir --mode=700 .ssh cat id_rsa.pub >> .ssh/authorized_keys
Now exit from the remote server's SSH session. You now need to run ssh-agent. However, if you have a blank passphrase, the following steps are not necessary and you may begin logging in to the remote server without a password.
If you did enter a passphrase, then execute the following commands:
eval `ssh-agent -s` ssh-add
It would also probably be a good idea to add a command to kill all ssh-agent processes to your shell's logout script (for example ~/.bash_logout) or else you may leave behind some stray processes.
echo killall ssh-agent >> ~/.bash_logout
You may now access the remote server via SSH in any way (such as using svn) without having to enter a password again. If you reboot or log out and log back in, you only have to run ssh-agent and ssh-add again.